Why monitoring customer and user activities matters
Lenders as financial services providers are mandated by law to track activities and the financial flow of money. Lendsqr provides the tools and methods to do these natively. This allows any lender to monitor the activities of their customers and users.
For instance, if a user claims that they never applied for a loan, you can easily trace their actions using the audit logs or the logs on the user’s profile page. This helps resolve any issues more quickly, as it can serve as proof of action.
The regulatory imperative for activity monitoring
Financial institutions operate under extensive regulatory frameworks designed to prevent fraud, money laundering, terrorist financing, and other financial crimes. These regulations impose specific obligations on lenders to know their customers, monitor transactions, and maintain detailed records of all activities occurring within their systems.
Know Your Customer or KYC regulations require lenders to verify customer identities and understand the nature of their activities. This goes beyond simply collecting identification documents during onboarding. You must continuously monitor customer behavior to detect unusual patterns that might indicate identity theft, account takeover, or other fraudulent activities.
Anti-Money Laundering or AML requirements mandate that lenders track the flow of funds through their platforms and report suspicious activities to relevant authorities. If a customer suddenly begins borrowing and repaying unusually large amounts, receiving transfers from unexpected sources, or exhibiting other anomalous financial behavior, you must be able to detect and investigate these patterns.
Transaction monitoring obligations extend to all financial movements, including loan applications, disbursements, repayments, wallet funding, transfers, and withdrawals. Comprehensive logs documenting each transaction with timestamps, amounts, involved parties, and other relevant details form the foundation of regulatory compliance.
Audit trail requirements mandate maintaining immutable records of all system activities that can be reviewed during regulatory examinations. When regulators audit your operations, they will request evidence demonstrating your compliance with various requirements. Detailed activity logs provide this evidence, showing that you properly monitored activities and responded appropriately to issues.
Consumer protection regulations also drive monitoring requirements. When customers dispute transactions or claim they never authorized certain actions, you must be able to investigate and provide evidence about what actually occurred. Without detailed activity logs, resolving disputes fairly becomes impossible.
Beyond compliance to operational benefits
While regulatory compliance provides the primary justification for activity monitoring, the operational benefits extend far beyond simply satisfying legal requirements.
Fraud detection and prevention improve dramatically when you can analyze customer activity patterns. Many fraud schemes involve subtle behavioral anomalies that only become apparent when you review comprehensive activity logs. A fraudster who has stolen login credentials might access the system at unusual hours, from unfamiliar locations, or attempt actions the legitimate user never performs. Activity logs reveal these patterns, enabling you to intervene before significant losses occur.
Dispute resolution becomes faster and more definitive with detailed activity logs. When a customer claims they never applied for a loan, never authorized a transfer, or never received a disbursement, you can review the exact sequence of events to determine what actually happened. Did they apply for the loan themselves or did someone else access their account? Was the disbursement sent but the customer’s bank had issues? Logs answer these questions conclusively.
Customer support quality improves when support agents can review a customer’s recent activities to understand context before addressing their questions. If a customer calls confused about a charge they do not recognize, the support agent can quickly review their recent transactions, identify what the charge relates to, and provide a clear explanation. This transforms confusing interactions into helpful ones.
System troubleshooting and debugging rely heavily on activity logs. When customers report errors or unexpected system behavior, your technical team needs to understand exactly what actions the customer took, in what sequence, and what the system response was at each step. Activity logs provide this critical information, enabling faster problem identification and resolution.
User experience optimization benefits from analyzing activity patterns across your customer base. By reviewing how customers navigate your application process, where they get stuck, what features they use frequently, and what features they ignore, you can identify improvement opportunities that make your platform more intuitive and efficient.
Security incident response depends on comprehensive logging. When you detect a security breach or unauthorized access, activity logs help you determine the scope of the incident, what data was accessed, what actions the intruder took, and how the breach occurred. This information is essential for containing the damage and preventing future incidents.
Understanding Lendsqr’s activity monitoring capabilities
Lendsqr provides native tools for monitoring customer and user activities without requiring additional integrations or third-party services. These built-in capabilities ensure every lender has access to comprehensive activity tracking regardless of their subscription tier or technical sophistication.
The platform maintains detailed logs of all user actions including login events, loan applications, document uploads, profile updates, transaction initiations, payment activities, and system interactions. Each logged event captures essential information such as the timestamp showing exactly when the action occurred, the user identity indicating who performed the action, the action type describing what was done, relevant details specific to that action type, the result showing whether the action succeeded or failed, and contextual information like IP address or device type.
These logs are stored securely and remain accessible for extended periods, ensuring you can investigate issues that occurred days, weeks, or even months in the past. The retention period depends on your subscription plan and regulatory requirements in your jurisdiction, but typically extends to at least several months and often years for critical financial transactions.
Accessing activity information through audit logs
The audit log provides a centralized view of all activities across your entire platform. This system-wide perspective enables you to search for specific events, filter by time period, user, action type, or other criteria, and analyze patterns across your customer base.
Audit logs serve multiple purposes. For compliance reporting, you can extract logs showing all transactions over a certain amount, all activities by specific high-risk customers, or all events during a particular time period. For fraud investigation, you can search for anomalous patterns like multiple failed login attempts, unusual transaction sequences, or activities from suspicious IP addresses. For operational analysis, you can review system usage patterns, identify features experiencing errors, or understand peak usage times.
The audit log interface typically provides filtering and search capabilities that let you narrow down the vast amount of logged data to find relevant events. You might search for all actions by a specific customer, all loan applications submitted on a particular date, all failed transactions, or all activities originating from a specific geographic region.
Accessing activity information through user profile logs
In addition to the centralized audit log, Lendsqr provides activity logs directly on each user’s profile page. This user-specific view shows all actions that a particular customer has taken within your platform.
The user profile log offers a chronological timeline of that customer’s journey through your system. You can see when they created their account, when they completed KYC verification, when they applied for loans, when disbursements occurred, when repayments were made, and every other significant event in their relationship with your lending platform.
This focused view is particularly valuable during customer support interactions. When a customer contacts you with a question or concern, pulling up their profile and reviewing their recent activity logs provides immediate context. You can see what they have been doing recently, identify any errors or failed transactions they might be asking about, and understand their situation without requiring them to explain everything from scratch.
Further reading: Reach more customers with the Lendsqr offline loan feature
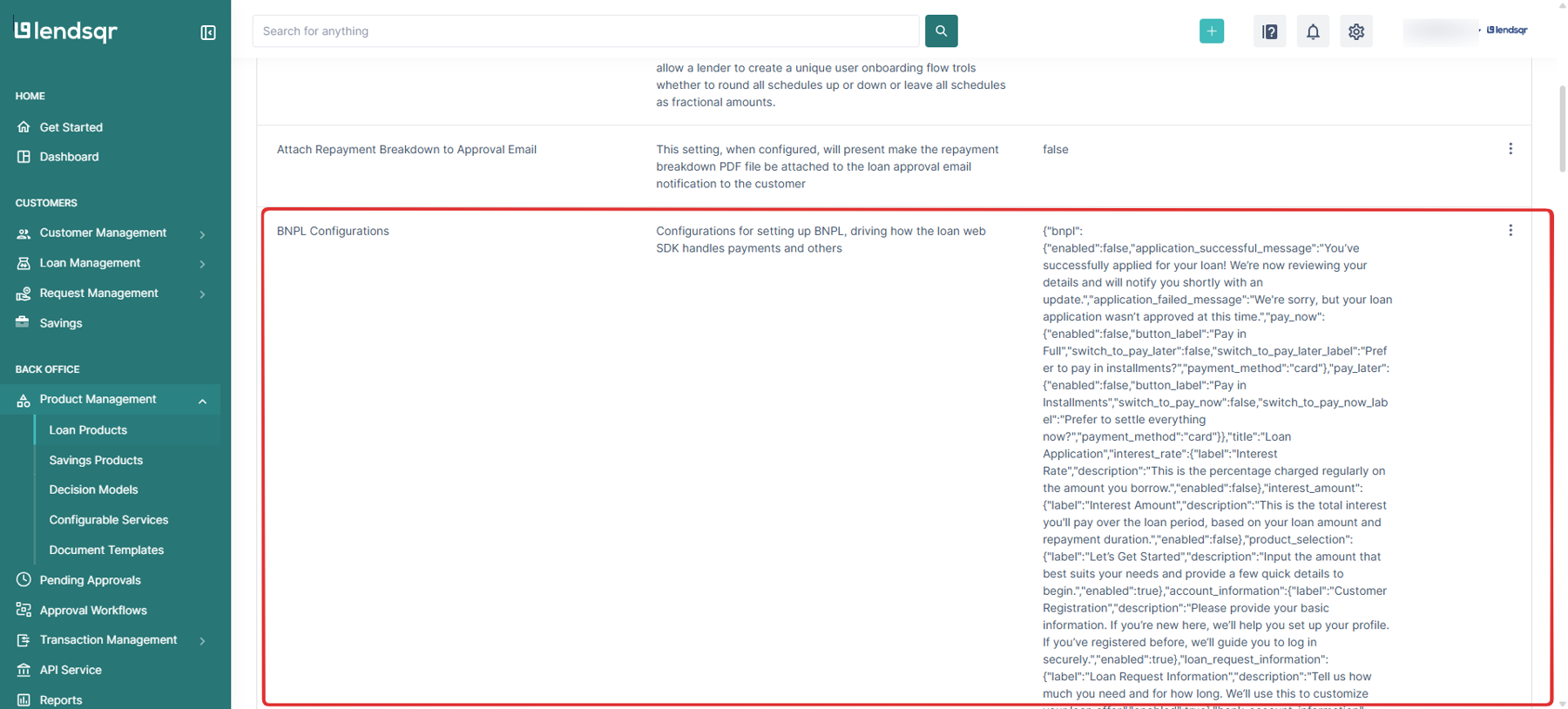
Step-by-step guide on how to view a customer’s activity from the admin console
1. You can view a customer’s activities directly from the audit log or from logs within the user’s profile page.

Read further: How to manage users logs
2. You can also view the details the logs on the user’s profile page.

Common use cases for activity monitoring
Understanding typical scenarios where activity logs prove valuable helps you leverage this capability more effectively in your daily operations.
Investigating disputed loan applications
A customer contacts you claiming they never applied for a loan that appears in their account. This could indicate fraud, account compromise, or simply customer confusion. By reviewing their activity logs, you can see the exact timestamp of the loan application, the IP address and device it came from, what information was submitted, and whether the session was authenticated with the customer’s credentials or through some other means. This evidence either confirms the customer did apply or reveals that unauthorized access occurred.
Tracing missing disbursements
A borrower claims they never received their approved loan disbursement. Activity logs show exactly when the disbursement was initiated, what payment method was used, what account number it was sent to, and whether the disbursement succeeded or failed. If the disbursement succeeded according to your system but the customer did not receive funds, the logs help you engage with payment processors or banks to trace the transaction through the financial system.
Identifying suspicious repayment patterns
Regulatory obligations and fraud prevention both require monitoring repayment activities. If a borrower suddenly begins making repayments from unfamiliar sources, at unusual times, or in unexpected amounts, activity logs highlight these anomalies for investigation. The pattern might indicate money laundering, use of stolen funds, or other concerning activities requiring further scrutiny.
Resolving access and permission issues
A user reports they cannot access certain features or perform specific actions. Activity logs show what they attempted to do, what error messages the system generated, and what their permission levels are. This information helps support teams quickly determine whether the issue stems from incorrect permissions, system errors, or user confusion about how features work.
Tracking regulatory compliance actions
When you take regulatory compliance actions like freezing accounts, blocking transactions, or reporting suspicious activities, detailed logs document exactly what actions were taken, when, by whom, and why. This documentation is essential when regulators review your compliance program or when you need to demonstrate you followed proper procedures.
Best practices for leveraging activity monitoring
To maximize the value of Lendsqr’s activity monitoring capabilities while maintaining customer privacy and operational efficiency, follow these best practices.
Regular review of high-risk activities
Do not wait for problems to surface before reviewing logs. Establish regular routines for reviewing activities by high-risk customers, large transactions, failed authentication attempts, and other events that warrant proactive monitoring. This proactive approach catches issues early before they escalate into serious problems.
Establish clear escalation procedures
Define clear criteria for what types of logged activities should trigger escalation to supervisors, compliance officers, or management. Not every unusual pattern warrants investigation, but certain combinations of factors should automatically trigger enhanced scrutiny. Document these criteria and train your team to recognize and respond appropriately.
Protect customer privacy
While activity monitoring is necessary for security and compliance, it must be balanced against customer privacy rights. Access to activity logs should be restricted to personnel with legitimate business needs. Log your own team’s access to customer logs so you can audit who viewed what information and when. Use logged data only for legitimate purposes related to operations, security, compliance, and customer support.
Integrate monitoring into support workflows
Train customer support teams to routinely review customer activity logs when handling inquiries. This practice provides context that improves support quality and resolution speed. However, ensure support agents understand what they are looking at and how to interpret log data correctly to avoid misunderstandings.
Document significant findings
When activity log reviews reveal important issues like fraud attempts, security breaches, compliance violations, or significant system errors, document your findings thoroughly. Create case files that include relevant log excerpts, analysis of what occurred, actions taken in response, and outcomes. This documentation supports regulatory compliance, aids future investigations, and helps identify systemic issues requiring broader solutions.
Maintain log integrity
Activity logs serve as evidence in disputes and regulatory examinations. Their value depends on their integrity and immutability. Never alter, delete, or tamper with log data except through proper retention policies applied uniformly. Implement access controls ensuring only authorized personnel can view logs and absolutely no one can modify historical log entries.
Use logs for continuous improvement
Beyond immediate operational uses, periodically analyze activity logs to identify improvement opportunities. What errors occur frequently? Where do customers get confused? What features are underutilized? What processes create friction? Log analysis reveals these patterns, guiding product improvements and process optimizations that benefit all customers.
Activity monitoring through comprehensive logging represents a critical capability that every modern lender must maintain. Lendsqr’s native activity monitoring tools provide the visibility you need to meet regulatory obligations, prevent fraud, resolve disputes, support customers effectively, and continuously improve your operations. By understanding these capabilities and leveraging them systematically, you transform compliance obligations into operational advantages that strengthen your lending business.